Sadogo ransomware removal instructions
What is Sadogo?
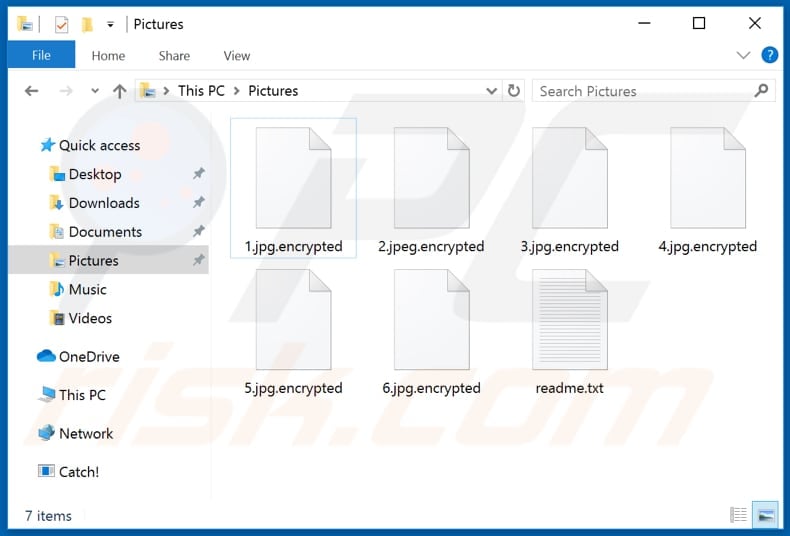
Sadogo was discovered by dnwls0719. It encrypts victim's files, changes their filenames by appending the ".encrytped" extension (e.g., it renames "1.jpg" to "1.jpg.encrypted", and so on) and generates ransom notes text files called "readme.txt". These ransom notes can be found in all folders that contain encrypted data, they contain instructions on how to contact Sadogo's developers.
In order to contact cyber criminals who designed Sadogo victims have to open the provided link with a Tor browser. That website contains a contact form where victims have to enter they name or a company name, email address and ID to contact Sadogo's developers. When contacted, cyber criminals should provide details such as price of a decryption software and/or key and how to pay for it. It is common that ransomware like Sadogo encrypts files with a strong encryption algorithm and the only way to decrypt files is to use tools that can be provided by cyber criminals who designed ransomware. Unfortunately, there are many cases where victims who paid a ransom got scammed - they had not received a decryption tool even after a payment. Typically, the only way to recover files without losing any money and risking to be scammed is to restore them from a backup. It is worthwhile to mention that ransomware can be prevented from causing possible further encryptions by uninstalling it from a computer. Although, files remain encrypted even after uninstallation.
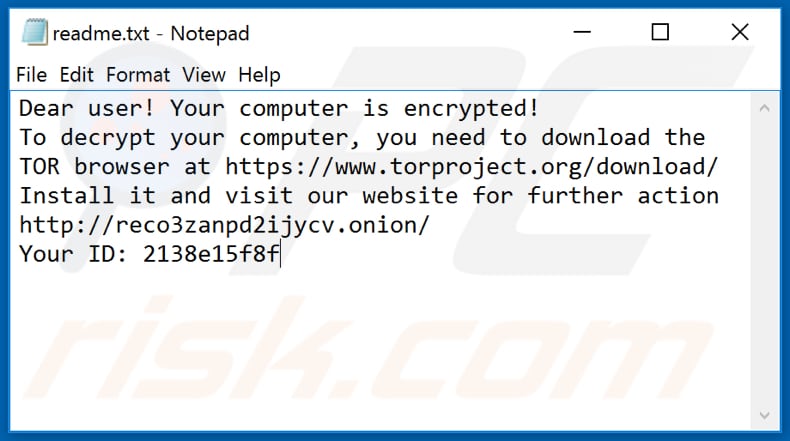
Screenshot of a message encouraging users to pay a ransom to decrypt their compromised data:
Usually malware of this type is designed prevent victims from accessing data by encrypting it and keep it inaccessible unless they decrypt it with a tool and/or key. Two most common and main variables are size of a ransom and encryption algorithm (symmetric or asymmetric) that ransomware uses to encrypt data. As a rule, decryption tools and/or keys can be purchased only from cyber criminals who designed a particular ransomware. It is possible to decrypt files without those tool only in cases when ransomware has some bugs, flaws. Unfortunately, it does not happen often. As mentioned in the previous paragraph, most of the times the only to recover files for free is to restore them from a backup. Therefore, it is recommended to always have data backup created and keep it on a remote server or unplugged storage device. Examples of programs that are categorizedas ransomware too are Love$, .waiting and .notfound.
How did ransomware infect my computer?
Some common methods to spread malware are by using spam campaigns, questionable file, software download channels, Trojans, fake software updating or unofficial activation tools. To spread malware via spam campaigns, cyber criminals send emails with malicious files attached to them. Their main goal is to trick recipients into opening a malicious attachments (or files downloaded through a provided links). When opened, those files install ransomware or other malware. Examples of files that cyber criminals can attach to their emails are Microsoft Office, PDF documents, JavaScript files, archive files like ZIP, RAR and executable files (like .exe). Untrustworthy software or file download channels such as unofficial, freeware download websites, free file hosting pages, Peer-to-Peer networks (e.g., eMule, torrent clients), and other similar tools can be used to proliferate malicious programs too. Cyber criminals succeed when users open malicious files that were downloaded through those channels. Trojans are malicious programs that can be designed to cause chain infections. It is common that when a Trojan is installed on a computer, then it installs additional malware. Fake, unofficial software updating tools infect systems installing malware instead of updates, or by exploitinh bugs, flaws of some outdated software that is installed on users computer. Unofficial activation ('cracking') tools are used by users who seek to activate licensed software for free. However, tools of this type often are designed by cyber criminals and cause installation of malicious software.
| Name | Sadogo virus |
| Threat Type | Ransomware, Crypto Virus, Files locker |
| Encrypted Files Extension | .encrypted |
| Ransom Demanding Message | readme.txt and Tor website |
| Cyber Criminal Contact | Chat on Tor website |
| Detection Names | Avast (FileRepMalware), BitDefender (Trojan.GenericKD.33688086), ESET-NOD32 (A Variant Of Win32/Kryptik.HCUR), Kaspersky (UDS:DangerousObject.Multi.Generic), Full List Of Detections (VirusTotal) |
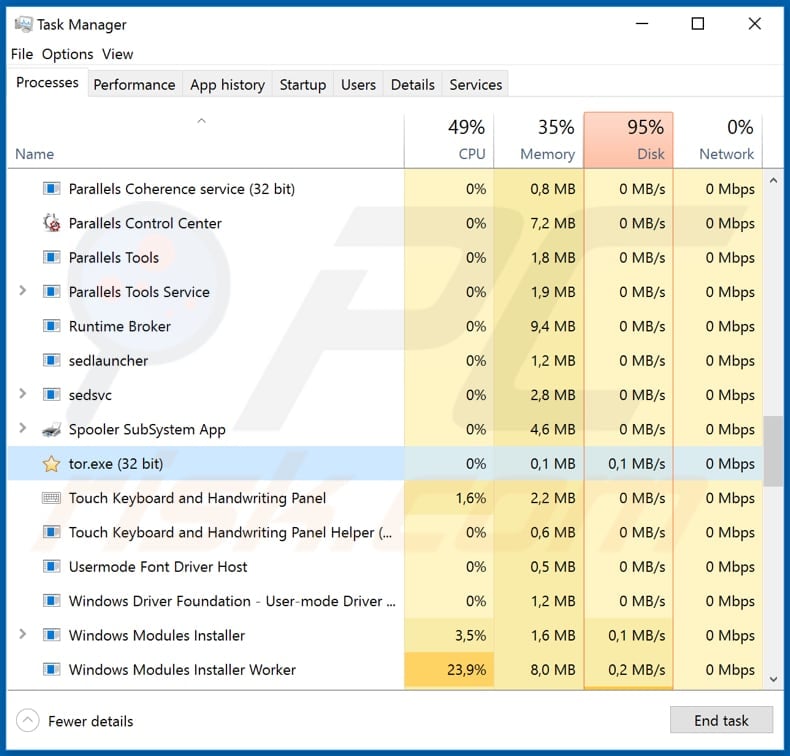
| Rogue Process Name | tor.exe (its name may vary) |
| Symptoms | Cannot open files stored on your computer, previously functional files now have a different extension (for example, my.docx.locked). A ransom demand message is displayed on your desktop. Cyber criminals demand payment of a ransom (usually in bitcoins) to unlock your files. |
| Distribution methods | Infected email attachments (macros), torrent websites, malicious ads. |
| Damage | All files are encrypted and cannot be opened without paying a ransom. Additional password-stealing trojans and malware infections can be installed together with a ransomware infection. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Spyhunter.
▼ Download Spyhunter To use full-featured product, you have to purchase a license for SpyHunter. Limited free trial available, subject to a forty eight hours waiting period. |
How to protect yourself from ransomware infections?
Website links and/or attachments that are included in emails should not be opened if there is any reason to believe that it may be not safe. It is worth mentioning that cyber criminals often disguise their emails as official, important, and so on. If an email is irrelevant, it is received from unknown, suspicious address, then its contents should be left unopened. All software (and files) should be downloaded from official, trustworthy websites. Any other sources should not be trusted. Examples of sources of this kind are mentioned in the previous paragraph. All installed software must be updated and activated through tools and/or functions that are designed (provided) by official software developers. This party, unofficial tools often are designed to distribute malicious programs. Also, it is not legal to activate licensed software with third party ('cracking') tools. And finally, it is important to regularly scan the operating system with an up-to-date reputable antivirus or anti-spyware software always remove detected threats as soon as possible. If your computer is already infected with Sadogo, we recommend running a scan with Spyhunter for Windows to automatically eliminate this ransomware.
Text presented in Sadogo ransomware's text file ("readme.txt"):
Dear user! Your computer is encrypted!
To decrypt your computer, you need to download the TOR browser at hxxps://www.torproject.org/download/
Install it and visit our website for further action hxxp://reco3zanpd2ijycv.onion/
Your ID: -
The appearance of Sadogo's Tor website (GIF):
Text in this website:
What happened
Your network has been infected!Your documents, photos, databases and other important files encryptedTo decrypt your files you need to buy our special software - General-DecryptorYou can do it right now. Use chat bellow. But remember that you do not have much time
Malicious Sadogo process running in Task Manager as "tor.exe" (its name may vary):
Screenshot of files encrypted by Sadogo (".encrypted" extension):
Sadogo ransomware removal:
Instant automatic malware removal:Manual threat removal might be a lengthy and complicated process that requires advanced computer skills. Spyhunter is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:▼ DOWNLOAD SpyhunterBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for SpyHunter. Limited free trial available, subject to a forty eight hours waiting period.
Quick menu:
- What is Sadogo?
- STEP 1. Sadogo virus removal using safe mode with networking.
- STEP 2. Sadogo ransomware removal using System Restore.
Step 1
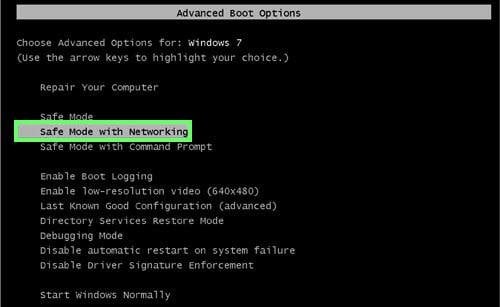
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.
Video showing how to start Windows 7 in "Safe Mode with Networking":
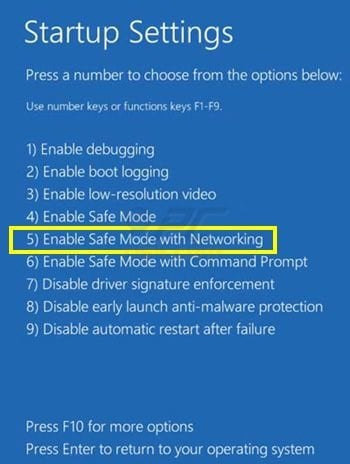
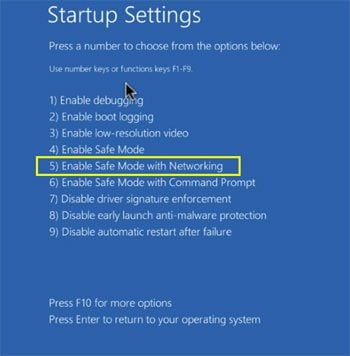
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup. Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings". Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.
Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options". In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.
Video showing how to start Windows 10 in "Safe Mode with Networking":
Step 2
Log in to the account infected with the Sadogo virus. Start your Internet browser and download a legitimate anti-spyware program. Update the anti-spyware software and start a full system scan. Remove all entries detected.
If you cannot start your computer in Safe Mode with Networking, try performing a System Restore.
Video showing how to remove ransomware virus using "Safe Mode with Command Prompt" and "System Restore":
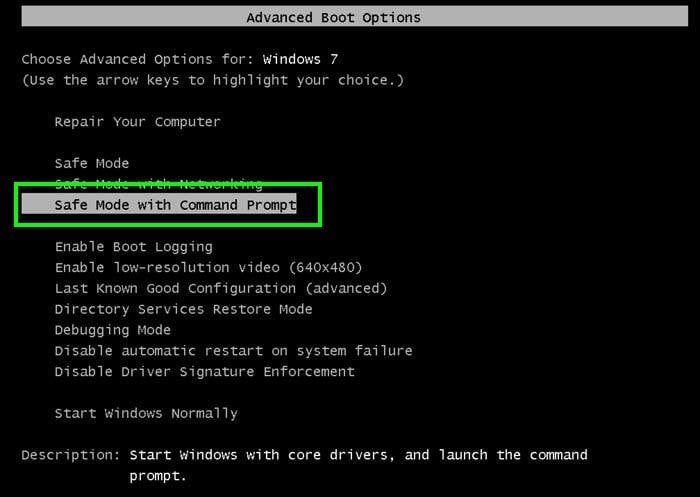
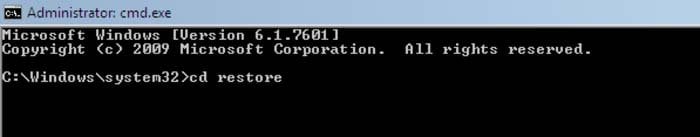
1. During your computer start process, press the F8 key on your keyboard multiple times until the Windows Advanced Options menu appears, and then select Safe Mode with Command Prompt from the list and press ENTER.
2. When Command Prompt mode loads, enter the following line: cd restore and press ENTER.
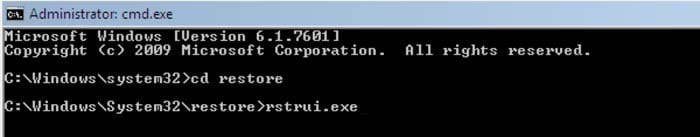
3. Next, type this line: rstrui.exe and press ENTER.
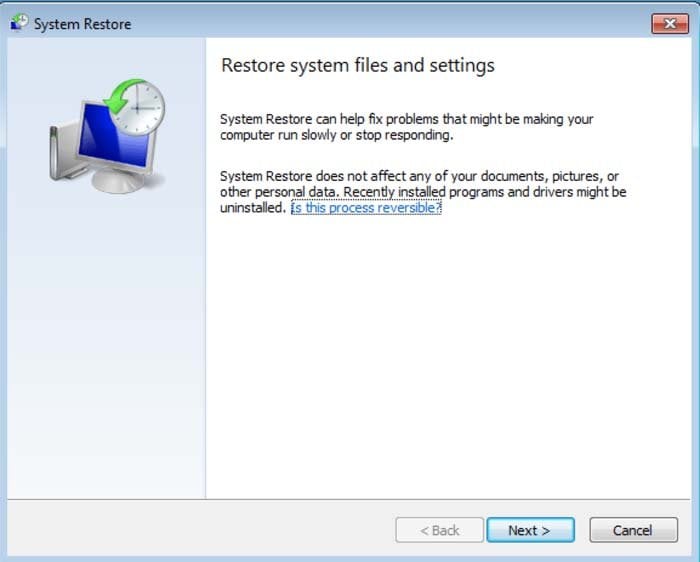
4. In the opened window, click "Next".
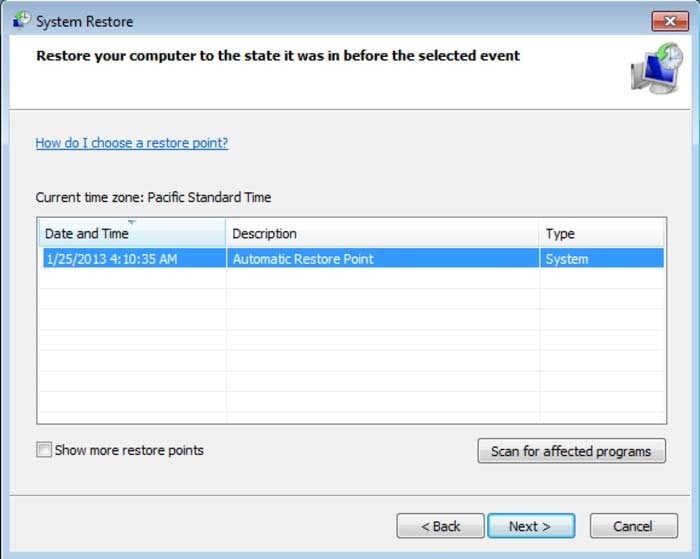
5. Select one of the available Restore Points and click "Next" (this will restore your computer system to an earlier time and date, prior to the Sadogo ransomware virus infiltrating your PC).
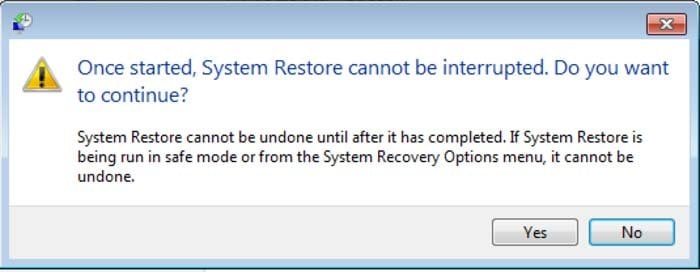
6. In the opened window, click "Yes".
7. After restoring your computer to a previous date, download and scan your PC with recommended malware removal software to eliminate any remaining Sadogo ransomware files.
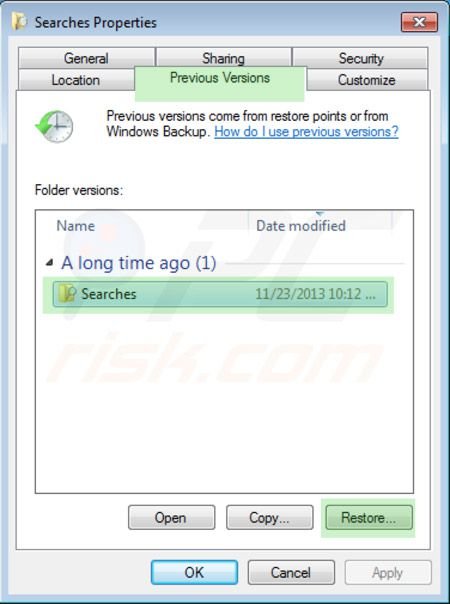
To restore individual files encrypted by this ransomware, try using Windows Previous Versions feature. This method is only effective if the System Restore function was enabled on an infected operating system. Note that some variants of Sadogo are known to remove Shadow Volume Copies of the files, so this method may not work on all computers.
To restore a file, right-click over it, go into Properties, and select the Previous Versions tab. If the relevant file has a Restore Point, select it and click the "Restore" button.
If you cannot start your computer in Safe Mode with Networking (or with Command Prompt), boot your computer using a rescue disk. Some variants of ransomware disable Safe Mode making its removal complicated. For this step, you require access to another computer.
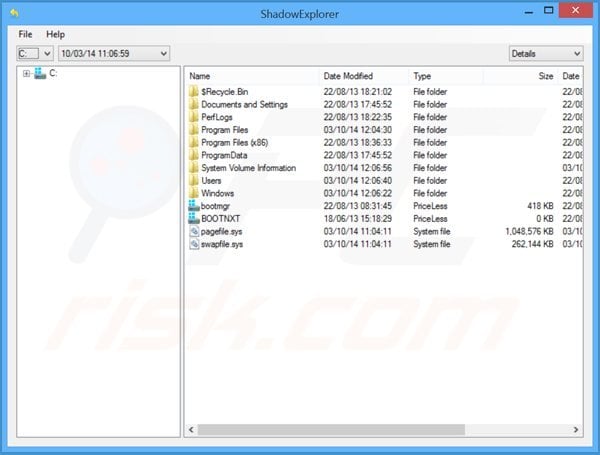
To regain control of the files encrypted by Sadogo, you can also try using a program called Shadow Explorer. More information on how to use this program is available here.
To protect your computer from file encryption ransomware such as this, use reputable antivirus and anti-spyware programs. As an extra protection method, you can use programs called HitmanPro.Alert and EasySync CryptoMonitor, which artificially implant group policy objects into the registry to block rogue programs such as Sadogo ransomware.
Note that Windows 10 Fall Creators Update includes a "Controlled Folder Access" feature that blocks ransomware attempts to encrypt your files. By default, this feature automatically protects files stored in the Documents, Pictures, Videos, Music, Favorites, and Desktop folders.
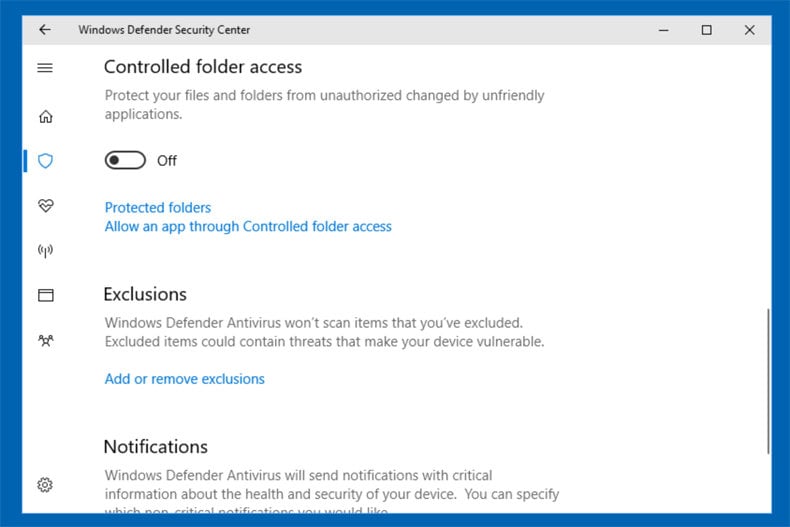
Windows 10 users should install this update to protect their data from ransomware attacks. Here is more information on how to get this update and add an additional protection layer from ransomware infections.
HitmanPro.Alert CryptoGuard - detects encryption of files and neutralises any attempts without need for user-intervention:

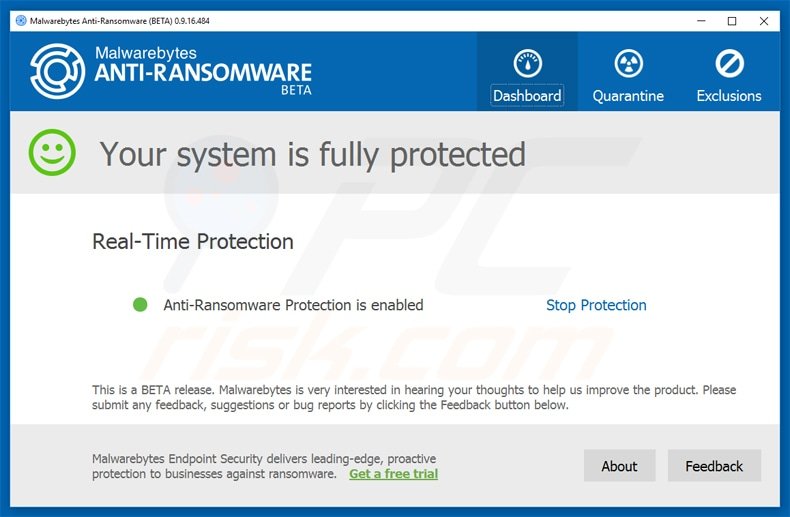
Malwarebytes Anti-Ransomware Beta uses advanced proactive technology that monitors ransomware activity and terminates it immediately - before reaching users' files:
- The best way to avoid damage from ransomware infections is to maintain regular up-to-date backups. More information on online backup solutions and data recovery software Here.
Other tools known to remove Sadogo ransomware:
Comments
Post a Comment